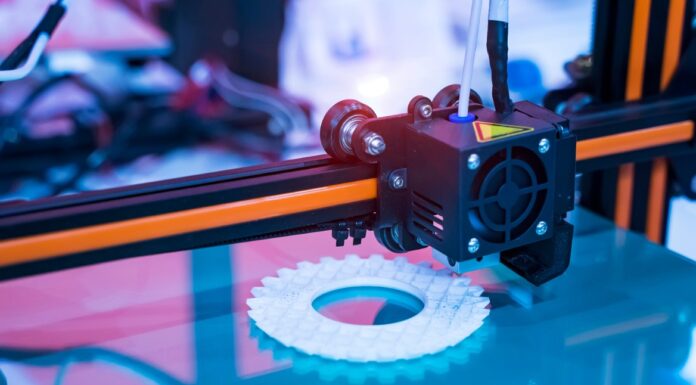
This article is by Steve Hunter, Senior Director for Systems Engineering, Forescout (Asia Pacific & Japan) Remote working has caused a rapid acceleration of digital transformation across most industries, with many moving forward into Industry 4.0. The manufacturing industry in particular has embraced the Internet of Things (IoT) to increase efficiency through automation and prepare…